Category: Theology Proper > The Existence of God > Special Revelation
Text: Hebrews 1:1–3; Psalm 19:7–11; 2 Timothy 3:16–17; John 1:1–14
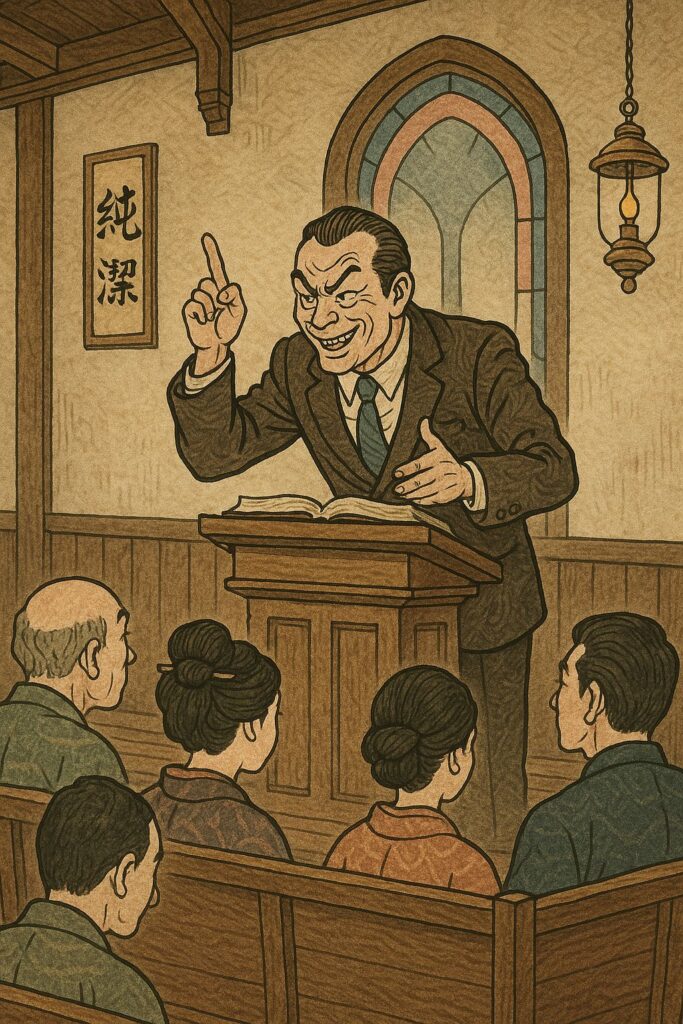
We learned how God speaks through creation, and while nature tells us that God exists, it does not tell us who He is, or how to be reconciled to Him. This is why God has spoken more clearly and specifically than just through nature, so to save the mankind. It is through His Word and through His Son, and this is called the special revelation while the message of His existence through nature is called the general revelation.
I. Definition
There are two ways that God reveals Himself:
- General revelation — in creation and conscience. It’s available to all people at all times (Romans 1:20). C. S. Lewis did an excellent job of explaining this, and he calls it the universal morality in his book Mere Christianity.
- Special revelation — in Scriptures, and ultimately in our Lord Jesus Christ. It is specific, verbal, and redemptive.
Romans 10:13-17 tells us tthat “faith comes by hearing, and hearing by the word of Christ.” You cannot come to saving faith through stargazing, feeling the sense of awe at Grand Canyon, or admiring a beautiful sunset. You must hear the Gospel—that Christ has died for our sins and resurrected—and that we confess our sins and accept Him as the Lord and Savior.
Throughout history, God has spoken to Adam in the Garden, to Noah to make a covenant with him, to Moses from the burning bush and on Mount Sinai, to Israel through many prophets, to the Church through the written Word, and to the whole world through His Son. God is not silent. He speaks that we may live.
II. God speaks through Scripture
Psalm 19, after marveling at the glory of creation, shifts in verse 7 to the glory of the Word:
“The law of Yahweh is perfect, restoring the soul; The testimony of Yahweh is sure, making wise the simple.” (v.7)
The psalmist describes God’s Word with seven terms: law, testimony, precepts, commandment, fear, judgments—and in each case it is perfect, right, pure, true, and eternal. More desirable than gold, sweeter than honey.
Why? Because it restores the soul. No sunset can do that.
Paul reinforces this in 2 Timothy 3:16–17:
“All Scripture is God-breathed and profitable… so that the man of God may be equipped for every good work.”
The Bible is not just a moral guidebook—it is the voice of God in written form. It teaches, corrects, and trains us to be holy. God Himself is speaking to us through His Word.
III. God speaks through his son
Now turn to Hebrews 1:1–3. Here is the climax of God’s speaking:
“God, having spoken long ago to the fathers in the prophets in many portions and in many ways, in these last days spoke to us in His Son…”
God once spoke in bits and pieces—through Moses, David, Isaiah—but now He has spoken fully and finally in Jesus.
Christ is not just the messenger—He is the message. He is the radiance of God’s glory and the exact imprint of His nature.
John 1:1 says,
“In the beginning was the Word, and the Word was with God, and the Word was God.”
And verse 14 declares:
“The Word became flesh and dwelt among us, and we saw His glory…”
Christ is the visible image of the invisible God (Colossians 1:15). To know Jesus is to know the Father. He exegetes God for us (John 1:18).
IV. The Necessity and Urgency of Special Revelation
This is not just theology—it’s life and death.
- People cannot be saved apart from the Gospel (Romans 10:14).
- The world does not need more vague spirituality—it needs the Word of God.
- And we, the Church, must proclaim it.
Hebrews 12:25 warns,
“See to it that you do not refuse Him who is speaking…”
God has spoken. We must listen, believe, and obey.
—
Special Revelation is the blazing center of God’s communication to us. Through Scripture, we have His words; through Jesus, we have His very heart.
God is not hidden. He is not silent. He has spoken to you in the Bible, and He has come to you in the flesh.
“Today, if you hear His voice, do not harden your hearts…” (Heb. 3:15)
Let us draw near, with reverence, repentance, and worship, to the God who speaks.